If you run a managed service provider business, you already know that a breach does not just affect you. It affects every client whose environment you touch. That is what makes MSPs one of the highest-risk categories in cyber underwriting, and one of the most underserved when it comes to coverage that is actually built for how they operate.
This article covers everything MSPs need to know about cyber insurance in 2026: why your exposure is fundamentally different from a typical small business, what coverage you actually need, what it costs, and what underwriters are looking for when they evaluate your application.
Why MSP cyber risk Is different
Most businesses face cyber risk in one direction: their own systems and data. MSPs face it in every direction at once.
You hold privileged access to dozens or hundreds of client environments. Your RMM, PSA, and remote access tools are, by design, the most powerful systems in your stack. That also makes them the highest-value targets for attackers. When a threat actor compromises an MSP, they do not get one victim. They get a master key.
Insurance carriers call this aggregation risk. A single incident at the MSP level can cascade across every client you manage. The liability exposure, contractual, legal, and financial, multiplies accordingly.
Recent litigation has made this concrete. In Travelers v. International Control Services, a carrier rescinded a $1 million cyber policy after a ransomware attack because MFA had only been enabled at the firewall, not across all systems as the application required. The court agreed. The policy was voided as if it never existed. For MSPs, the lesson is sharp: the security posture you represent on an application has to match the security posture you actually operate.
The two policies every MSP needs
Cyber liability insurance
Cyber liability covers the financial fallout from a security incident, both the costs you incur directly and the claims third parties bring against you.
First-party coverage (your costs) includes:
- Forensic investigation and incident response
- System restoration and data recovery
- Business interruption and lost revenue during downtime
- Ransomware extortion payments (where permitted by law)
- Crisis communications and public relations
- Regulatory fines and penalties
Third-party liability coverage (claims against you) includes:
- Legal defence costs when clients sue following a breach
- Settlements and judgments arising from compromised client data
- Regulatory defence if a client breach triggers an OCR, FTC, or state AG investigation
- PCI DSS fines and card brand assessments
For MSPs specifically, the third-party liability component is the critical one. Your clients' damages do not stay with your clients. They come back to you under your MSA, often under theories of negligence, breach of contract, and failure to perform.
Tech E&O insurance
Technology Errors and Omissions covers claims arising from your professional services, not just security incidents but failures in your work product. If a bad script wipes client file shares, if a botched migration corrupts data, if your team misses an SLA that causes a client financial harm, that is a Tech E&O claim, not a Cyber claim.
MSPs routinely need both. Cyber handles the attack-driven scenarios. Tech E&O handles the professional failure scenarios. The exposure that falls between them, a misconfiguration that also causes a data exposure for example, is where having both policies properly coordinated matters most.
What cyber insurance actually costs for MSPs
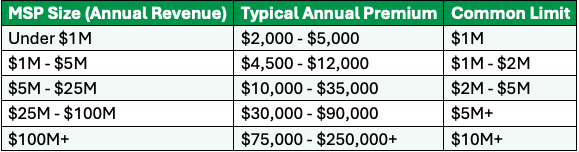
MSP premiums sit meaningfully above the market average because of aggregation risk and elevated claims frequency in the managed services category. Here is what current market data shows:
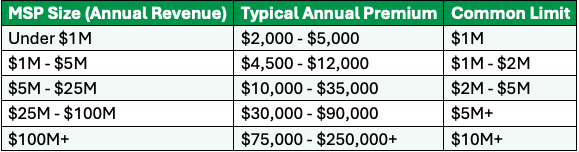
Source: SeedPod Cyber underwriting data and 2025-2026 broker benchmarks. Premiums assume standard limits and a clean loss history.
The biggest premium driver beyond revenue is your security stack and how well you can document it. An MSP with strong controls, MFA on all remote access, EDR on every endpoint, immutable backups with tested restores, and PAM in place, can see 20 to 35 percent better pricing than a peer of identical size with weak or undocumented controls.
If you are renewing a policy written two or three years ago without re-marketing it, there is a meaningful chance you are overpaying. The market shifted significantly since 2022's pricing peak. Clean MSP accounts with strong documented posture are seeing competitive pricing today.
What underwriters look For in MSP applications
In 2026, cyber underwriting has moved decisively away from checkboxes and toward verified evidence. For MSPs, that means demonstrating with exports, screenshots, and reports from your own toolset that the controls you claim are actually in place.
RMM and remote access hardening
Your RMM is your highest-risk attack surface. Underwriters want to see:
- MFA enforced on all RMM access, including technician accounts
- No open RDP exposed to the internet
- Role-based access controls limiting who can deploy scripts or push changes
- Audit logging enabled and retained
- Multi-person approval or change controls for high-impact actions
The Stryker breach, where attackers weaponised Microsoft Intune against the organisation's own endpoints, made MDM and RMM hardening a primary underwriting focus in 2026. If your RMM console is protected by a single password with no MFA, expect hard questions.
Separation of your infrastructure from client infrastructure
Underwriters evaluate whether a compromise of your own environment can cascade into client environments. Clean network segmentation, separate credential stores for client access, and documented offboarding procedures all support favorable terms.
Aggregation controls
How many clients would be affected if your management plane were compromised? Underwriters increasingly ask about maximum single-event exposure. MSPs that can demonstrate architectural controls limiting blast radius, such as network segmentation, isolated management VLANs, and per-client credential vaulting, are viewed more favorably than those with flat architectures.
Standard security controls (non-negotiable)
- MFA everywhere: email, VPN, RMM, PSA, and all admin accounts
- EDR on all endpoints: servers and workstations, with 24/7 monitoring or MDR
- Offline or immutable backups with tested restores, not just backup jobs running
- Email security: gateway or API-based filtering, DMARC enforced, phishing simulations documented
- Patch management: documented SLAs for critical patches, tracked in your PSA
- Incident response plan: written, current, and tested via tabletop in the last 12 months
The MSA problem: where most MSPs are exposed
Your Master Service Agreement is a liability document as much as it is a service document. Standard MSA boilerplate creates three common coverage gaps.
Unlimited liability language. If your MSA does not cap your liability to the client, a single large breach claim can exceed your policy limits. Courts have upheld client claims running well past what an MSP's policy covers when there is no contractual cap.
No requirement for client cyber insurance. If your client does not carry their own cyber coverage and suffers a breach, they have limited recovery options, which often means coming after you. Requiring clients to carry cyber insurance as a condition of service is one of the most effective ways to limit MSP exposure, and underwriters increasingly treat it as a positive control.
Ambiguous responsibility language. "We will use commercially reasonable efforts to maintain security" is not a defensible standard in litigation. Specific, documented security responsibilities, what you do, what the client is responsible for, and how incidents are handled, create a much cleaner picture for both defence counsel and your carrier.
Using cyber insurance requirements to grow MRR
One of the most underutilised aspects of cyber insurance requirements is the business case they create for upselling security services.
When a client sees MFA, EDR, and immutable backups as requirements on an insurance application rather than just recommendations from their MSP, the conversation changes. The requirement carries third-party authority. The client has skin in the game. Every tool or service you deploy to help them meet those requirements becomes MRR on your books.
The MSPs that grow fastest in this environment are the ones who position themselves as trusted risk advisors, not just IT vendors. That means leading QBRs with the insurance angle, documenting client security posture against underwriting requirements, and helping clients understand that their insurability directly depends on the stack you are recommending.
Common MSP cyber insurance mistakes
Buying a generic small business policy. Most off-the-shelf cyber policies are not designed for the aggregation risk MSPs carry. Key exclusions around services provided to third parties can leave you with no coverage for your largest actual exposure.
Misrepresenting controls on the application. If MFA is not deployed everywhere your application says it is, a carrier can rescind coverage after a claim. Apply accurately, then document.
Not coordinating Cyber and Tech E&O. The two policies need to work together. Coverage gaps and finger-pointing between carriers on dual-trigger events are a real problem when policies are not purchased and coordinated thoughtfully.
Auto-renewing without re-marketing. The market has moved. A policy written at 2022 peak rates should be benchmarked every renewal cycle. If your revenue, client count, or security posture has changed, your premium should too.
Setting limits based on budget, not exposure. A $1M policy sounds like a lot until you are staring at a multi-client breach response. Limits should be calibrated to your actual aggregated client exposure, not just what seems affordable.
How direct underwriting changes the equation for MSPs
Most cyber insurance for MSPs flows through retail brokers who are not specialists in the space. Direct underwriters can access the market more efficiently, reduce back-and-forth on evidence, and build programmes that reflect how MSPs actually operate, including structures that allow MSPs to embed insurance guidance into their client service model.
Integration with tools MSPs already use, such as ConnectWise and N-able, reduces the friction in getting clients quoted without leaving existing workflows. That operational fit matters when you are managing dozens of client accounts.